Infrastructure as Code (IaC) with Terraform: Building a Multi-Tier Architecture on AWS
Aspiring DevOps Engineer with hands-on experience in cloud platforms, automation, CI/CD pipelines, containerization, and infrastructure as code. Skilled in AWS, Docker, Kubernetes, Terraform, Ansible, and modern monitoring tools. Experienced with Linux administration, cPanel hosting environments, and deployment workflows. Additionally trained in full-stack development using React and FastAPI.
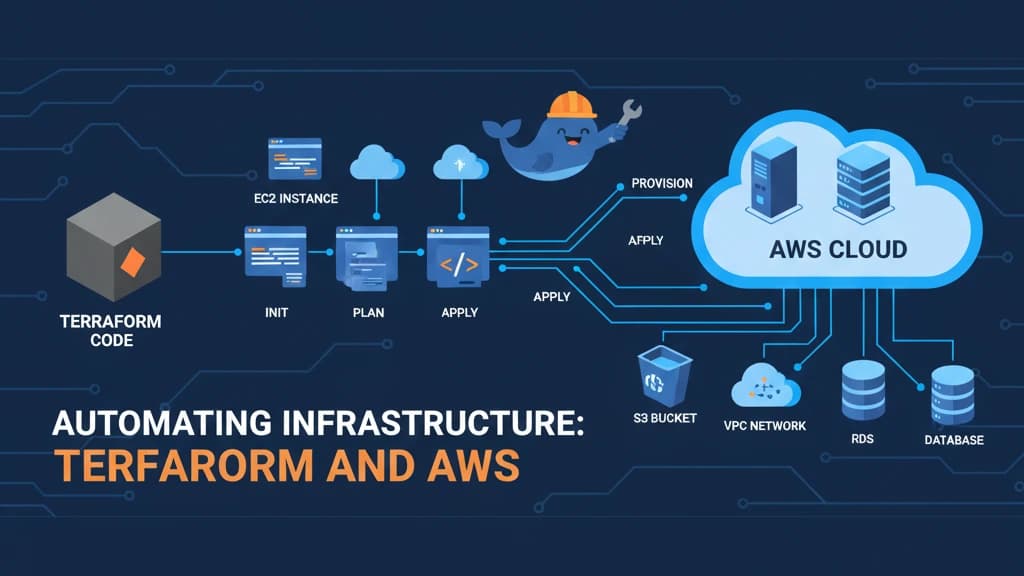
Infrastructure as Code (IaC) has revolutionized how we manage and provision cloud resources. In this post, I'll share my experience building a multi-tier architecture on AWS using Terraform.
Why Terraform?
Terraform provides several advantages for infrastructure management:
Declarative syntax - Define what you want, not how to get there
State management - Track infrastructure changes over time
Multi-cloud support - Work with AWS, Azure, GCP, and more
Reusable modules - Build once, use everywhere
Project Architecture
The multi-tier infrastructure includes:
VPC with public and private subnets
Application Load Balancer for traffic distribution
Auto Scaling Groups for EC2 instances
RDS database in private subnet
S3 buckets for static assets
CloudWatch for monitoring
Key Terraform Concepts
Resource Blocks
resource "aws_instance" "web" {
ami = var.ami_id
instance_type = "t3.micro"
tags = {
Name = "WebServer"
Environment = var.environment
}
}
Variables and Outputs
Using variables makes your infrastructure reusable:
variable "environment" {
description = "Environment name"
type = string
default = "production"
}
output "load_balancer_dns" {
value = aws_lb.main.dns_name
}
Best Practices
1. State Management
Always use remote state with locking:
terraform {
backend "s3" {
bucket = "terraform-state-bucket"
key = "prod/terraform.tfstate"
region = "us-east-1"
dynamodb_table = "terraform-locks"
encrypt = true
}
}
2. Module Structure
Organize your code into reusable modules:
terraform/
├── modules/
│ ├── vpc/
│ ├── compute/
│ └── database/
├── environments/
│ ├── dev/
│ └── prod/
└── main.tf
3. Security Considerations
Use IAM roles instead of access keys
Enable encryption at rest and in transit
Implement least privilege access
Use AWS Secrets Manager for sensitive data
Deployment Workflow
Initialize and Plan
terraform init
terraform plan -out=tfplan
Apply Changes
terraform apply tfplan
Destroy Resources
terraform destroy
Lessons Learned
Start small and iterate - Begin with basic resources and gradually add complexity
Use workspaces - Manage multiple environments efficiently
Version control everything - Track all infrastructure changes in Git
Test before production - Use terraform plan to preview changes
Document your modules - Clear documentation saves time
Monitoring and Cost Optimization
Implement CloudWatch alarms for:
EC2 CPU utilization
RDS connections
ALB response times
Auto Scaling events
Use AWS Cost Explorer and tags to track infrastructure costs per environment.
Conclusion
Terraform and AWS provide a powerful combination for infrastructure automation. By following IaC best practices, you can achieve reproducible, scalable, and maintainable infrastructure deployments.
The key is to start simple, build incrementally, and always keep security and cost optimization in mind.
Repository: Check out the complete code on GitHub with detailed setup instructions.